Introduction
|
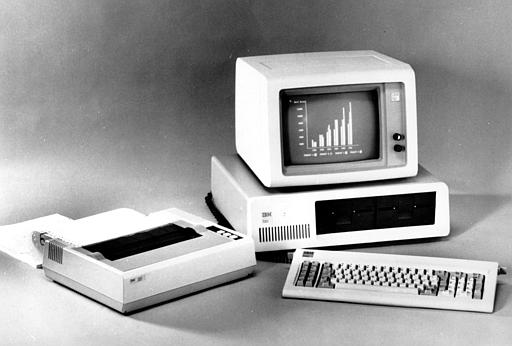
Once
upon a time, before the advent of the Internet and the
World Wide Web,
computers were
stand-alone, self-existing machines. Sharing
information and research often required traveling to national conferences to present
papers and/or having one's work published in scholarly books
or journals, a time-consuming and labor-intensive process, to say the least.
|
|||
| In those days, computer security at most college and universities involved locking one's office before leaving campus; a typical network administrator may have been responsible for telephone systems and not much more; the term information technology (IT) had not yet been coined; and acceptable use was a polite way of discouraging faculty and staff from tying up the office photocopier with personal tasks. |
|
|||

|
Today, computing and technology establish the framework upon which the core of an institution's educational infrastructure rests. The task of managing issues such as access rights, privacy, network security and copyright protection has evolved into an industry, with IT professionals playing an important role in shaping teaching and learning initiatives. | |||
| T o help manage complex IT systems, most colleges and universities have implemented IT policies that define the rules governing the use of these digital and electronic resources. These documents come in all shapes and sizes. |

|
|||

|
Although there is no consensus among higher education IT professionals about an "ideal" policy, what is certain is that these statements need to be embracive, enforceable and flexible in order to provide reliable computing services; allow for future advances in technology; protect the educational community from network security risks; and, at the same time, promote academic research and scholarship. | |||
| Back to top of page | Home | |||